In this Article
What Is an Anonymous Proxy and How Does It Work?
An anonymous proxy is like other types of proxies that make a user’s activity unnoticed on the web. It typically removes a user’s real IP address and changes it to the proxy’s IP. The most well-known cases, when DataImpulse anonymous proxies are used, are private web scraping, regional targeting, account management, and market research.
Key Facts
- An anonymous proxy hides the real IP of a user and replaces it with another one.
- The website recognizes the proxy IP instead of the original one and returns the response through the proxy back to the user.
- There are three levels of proxy anonymity: transparent, anonymous, and elite.
- Residential and mobile proxies are more difficult to get caught than datacenter proxies.
- IP reputation, headers, leaks, and unusual behavior are proxy detection methods.
- Common use cases include geo-targeting, multi-accounting, and web scraping.
- DataImpulse has its own pool of ethical residential IPs and presents coverage for 195 countries. Geo-targeting is included. Pay only for the traffic you use.
What is an anonymous proxy
An anonymous proxy makes user activity less visible. Unlike elite proxies, it still shows the website that the request is going through the proxy server. Transparent proxies show both the original IP and the fact that the proxy is used.
How an anonymous proxy server works
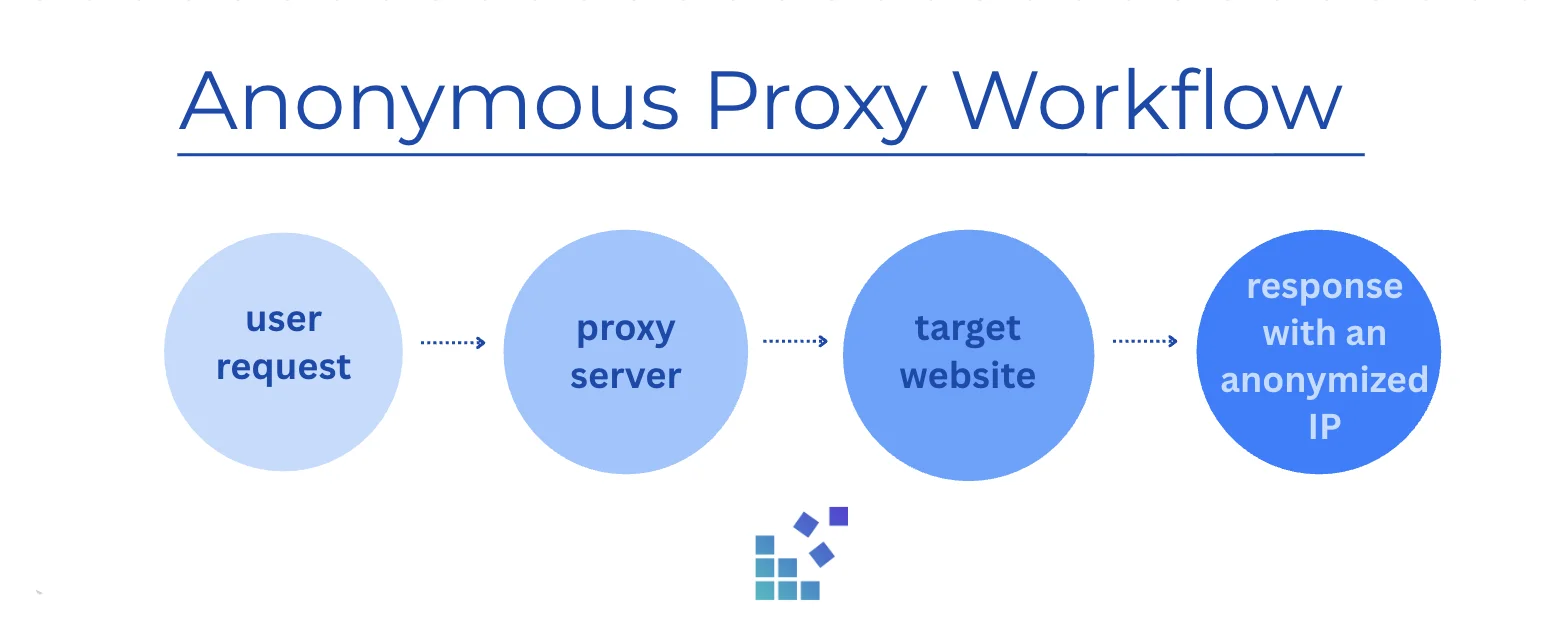
When a user connects via an anonymous proxy, their request doesn’t go directly to the target website. The process works through an intermediary server.
- User sends an HTTP request from the app or browser.
- An anonymous proxy server gets the request before it reaches the target site.
- Proxy forwards the reply to the destination website using its own IP address.
- The website handles the request and sends the response back to the proxy server.
- User gets the response from the proxy.
However, the anonymous proxy can include certain HTTP headers that indicate the connection is going through the proxy server. For example, Via or X-Forward-For headers.
Levels of proxy anonymity
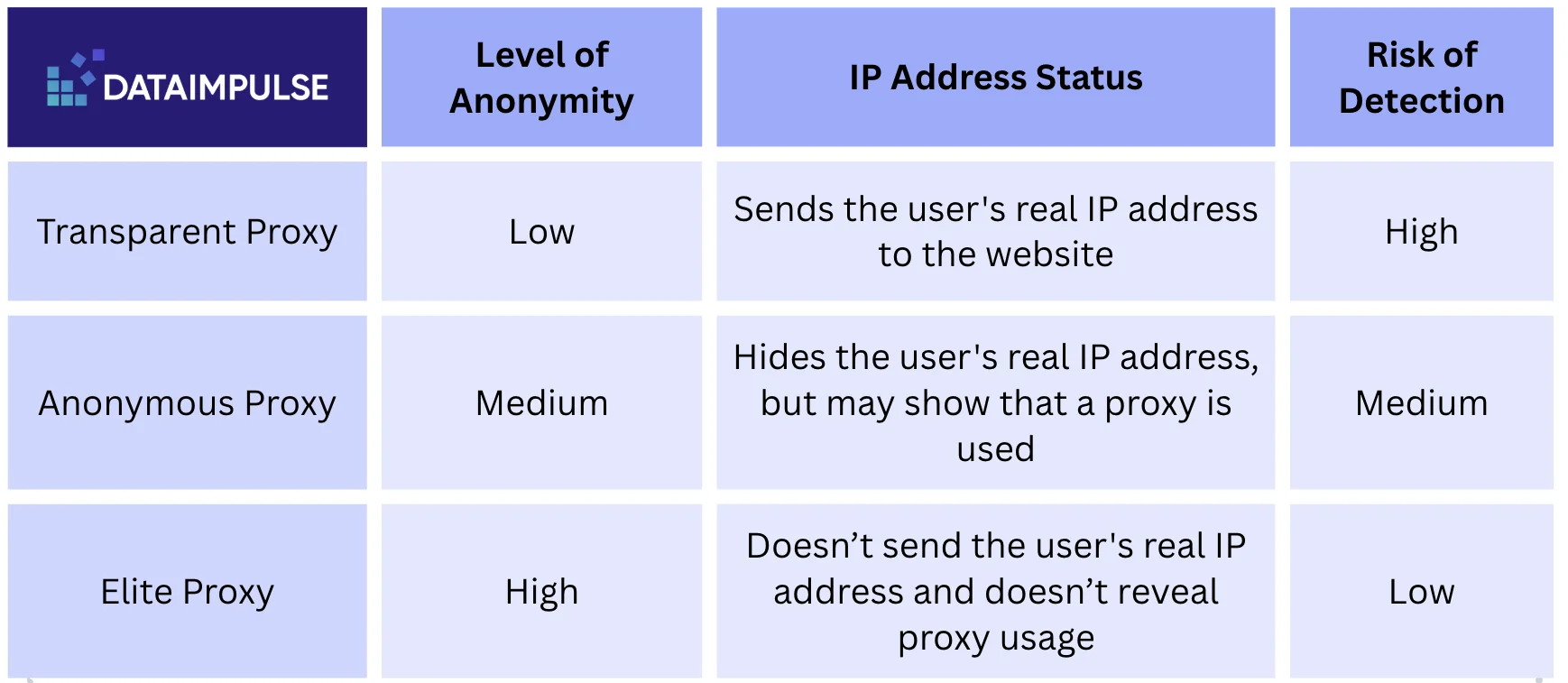
Not all proxy servers guarantee the same degree of privacy. It depends on how they handle network traffic and headers. Some proxies simply forward requests and expose the original IP address of a user. Others can hide the IP, but still show that a third-party server is involved. The most privacy-focused types mask the IP and make the connection look direct.
1. Transparent proxies
They are believed to have the lowest level of anonymity. The main reason is that transparent proxies don’t hide the user’s real IP address and often add HTTP headers that are a clear indicator of proxy usage.
2. Anonymous proxies
These proxies are medium in terms of anonymity. The original IP address is not visible, but the target website can still detect that the connection is coming from a proxy server.
3. Elite (high-anonymity) proxies
Elite proxies don’t reveal that a proxy has been used and mask the real IP address at the same time. In this case, the connection seems authentic. That’s why they are considered to have the highest level of anonymity.
Why people use anonymous proxies
Individuals and companies use anonymous proxies when they don’t want the global web to trace their activity online. This tool helps to reduce the amount of information websites can collect about connections. Another reason to use ‘anonymizers’ is having the opportunity to access web data in any location that may have connection issues for some reason. With DataImpulse proxies, users can change location signals, stay anonymous while browsing, route their connection through different regions, and scrape the data they desire.
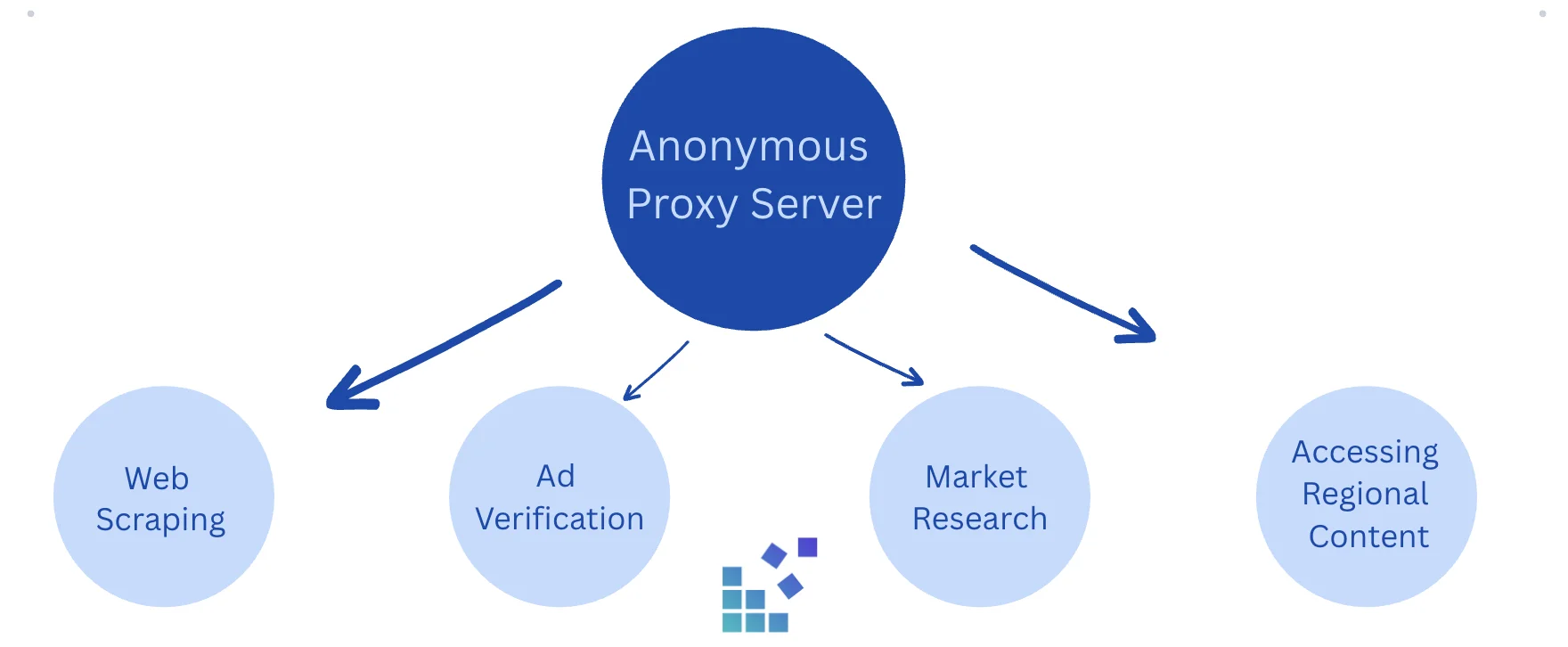
Common use cases for anonymous proxies
Anonymous proxies are used in many business and personal situations, especially when direct access to the target website can be limited. Businesses can collect various data, monitor competitors, test ad campaigns, and access content from any region. Individuals usually rely on these proxies to browse with more privacy and open websites unavailable in their country.
Web scraping and data collection
When a large number of requests come from one IP address, some websites may slow down the connection or block it entirely. Proxies lower the risk of getting caught as they distribute requests across multiple network addresses.
Ad verification
Since ad distribution may change depending on the location, anonymous proxies ensure users view the same page via a local IP. Proxy integration may help companies detect ad fraud on time and make sure their ads appear to the intended audience.
Market research
Businesses can compare prices, check what their potential competitors do, track local trends, and analyze how products are presented in different regions. Using IP addresses from other regions helps avoid geographic barriers while collecting information.
Accessing content from any region
There are some online services that are available only in certain countries. Anonymous proxies let users connect through an IP number in the required location and get the necessary data.
What does ‘anonymous proxy detected’ mean
The message ‘anonymous proxy detected’ can appear when a website recognizes that a connection comes through a proxy server, not from the user’s device. It doesn’t mean that there is an issue with the proxy itself. It means that the website has detected signs of proxy usage, such as uncommon HTTP headers or traffic patterns.
There are some websites that use security and anti-fraud systems to spot proxy connections. These systems protect against spam, account abuse, and lots of automated requests. If an anonymous proxy is detected, the website may limit some actions.
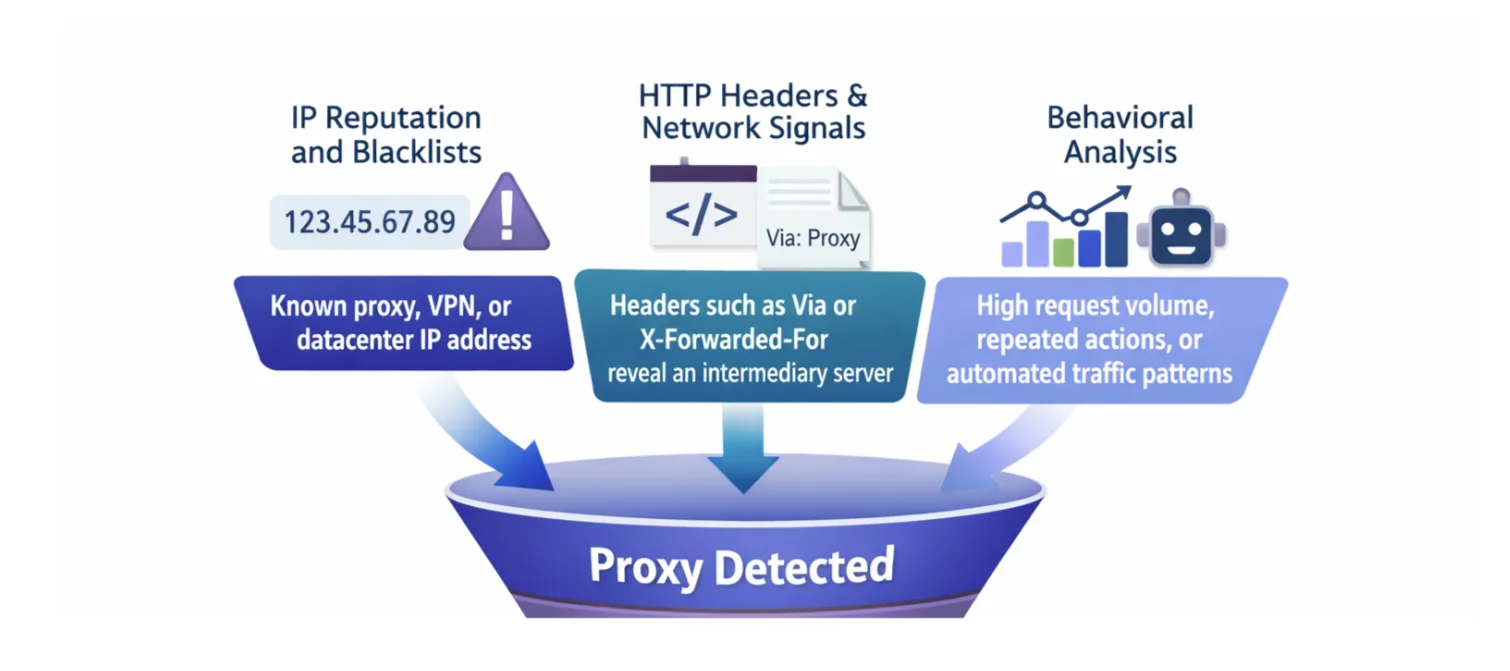
How websites detect anonymous proxies
Actual detection is based on technical signals that make the connection look different from normal user traffic. These indicators may be related to IP number, the HTTP headers included in the request, or the overall pattern of network activity.
IP Reputation and Blacklists
One of the most common detection methods is IP reputation. Websites rely on databases that contain lists of known proxies or VPNs. If the incoming IP address appears in one of these databases, the site may flag the connection as a proxy.
HTTP Headers and Network Signals
Proxy servers sometimes add HTTP headers such as Via, X-Forwarded-For, or Forwarded. These headers may reveal that the request passed through another server before reaching the website. Companies can also detect modifications in network routing, or mismatches between the user’s current location and other connection details.
Behavioral analysis
Many websites monitor the frequency of requests, how quickly pages are loaded, and whether the traffic follows a natural browsing pattern. For example, sending hundreds of requests in a brief amount of time or performing actions faster than a real user could may indicate automated activity. In this situation, the connection may be identified as suspicious and treated like a bot.
Types of proxies that can provide anonymity
Various types of IP infrastructure can be used to create anonymous proxies. While all of them conceal the user’s actual IP address, factors such as trust level, speed, cost, and detectability vary based on the underlying proxy network.
-
Residential proxies
Residential proxies are certain IP addresses assigned by Internet Service Providers to real users. They get through on sites that block datacenter traffic – rotating through 90M+ means each request comes from a different home address. These proxies have one of the highest levels of trust among customers. DataImpulse residential proxies start at $1 per GB.
-
Datacenter proxies
Datacenter proxies send requests through IP addresses from server networks. They are cheap, the price of DataImpulse datacenter proxies is $0.50 per GB. The responses are fast. Yet, because these IP addresses come from data center ranges, some target websites can detect and block them.
-
Mobile proxies
Mobile proxies send requests via IP addresses allocated by mobile operators on 3G, 4G, 5G, and LTE networks and provide traffic patterns identical to real mobile users. These proxies offer a high level of anonymity, and websites don’t flag them.
How to set up an anonymous proxy
Configuring an anonymous proxy is generally straightforward. Typically, users only require the proxy server’s IP address, port number, and occasionally login credentials. The specific process varies depending on whether the proxy is set up in a browser or within an application.
Browser configuration
One of the simplest methods to use an anonymous proxy is to set it up directly in a browser or operating system. Most browsers let users input the IP address and port of the proxy server within the network or connection settings. After getting the proxy details from a provider, users generally enter:
- Proxy IP address
- Port number
- Type of protocol, such as HTTP, HTTPS, or SOCKS5
After saving the configurations, all browser activity will be directed through the proxy server instead of the user’s actual connection. This way, websites will identify the proxy IP address instead of the user’s real one.
Certain operating systems also provide the option for a system-wide proxy configuration. In this scenario, not only the browser but also many other apps can integrate the proxy.
Proxy authentication
Some proxy servers require authentication before allowing access. Users can complete this step by simply entering the username and password provided by the proxy service. After all the credentials are verified, users connect to the proxy network through the anonymous proxy server and can route their traffic through it. Authentication is an important step as it protects the proxy company from unauthorized and illegal access. There is also an IP authentication. In this case, users add their own IP number to an approved list so the server can automatically recognize the connection and grant access.
Are anonymous proxies legal
Yes, anonymous proxies are legal in most countries. There is no harm from a proxy server that just routes internet traffic via another IP address. Businesses use anonymous proxies for privacy and security. However, the rightfulness of an anonymous proxy depends on how it is used. Scraping publicly available data, managing accounts, testing ads, or targeting – these are all legal cases for using proxies. If a proxy is used for illicit activities like fraud or violating laws, then it is not legal. Always comply with the terms of service and rules of the website you visit.
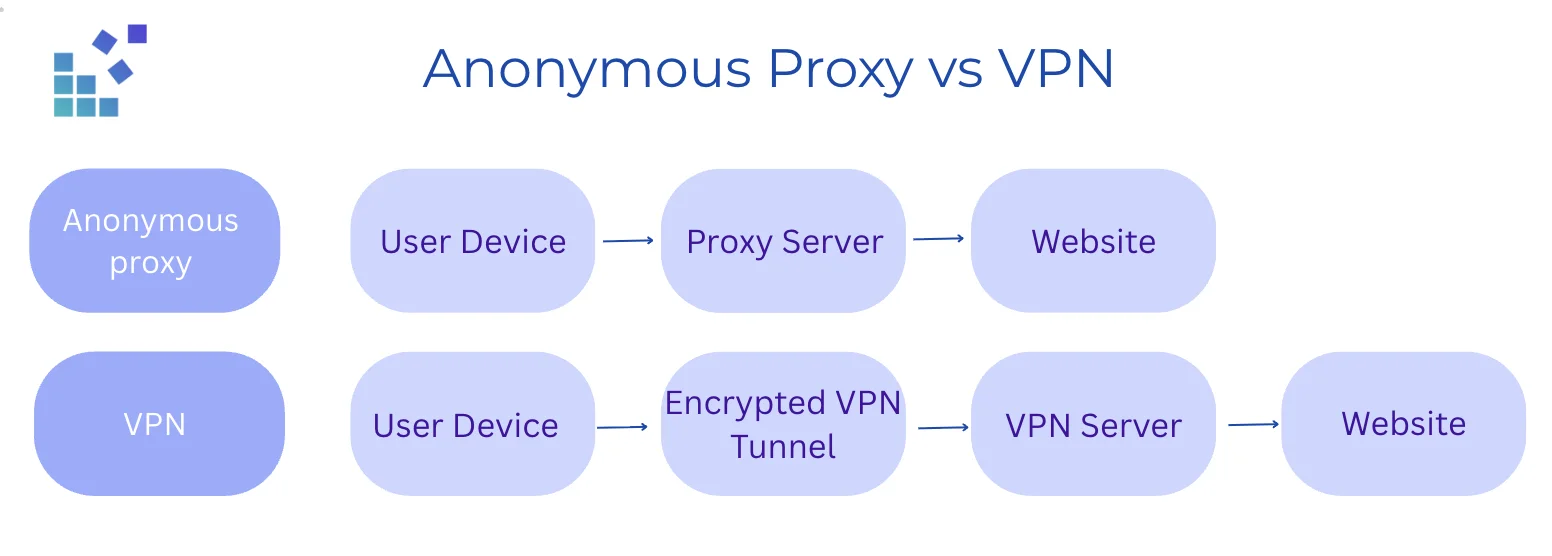
Anonymous proxy vs VPN
Proxy and VPN work differently and provide separate levels of protection. An anonymous proxy directs traffic from a particular browser or application via a different IP address. Then, websites detect the proxy IP address in place of the user’s actual one. A VPN, or a Virtual Private Network, makes an encrypted connection between the user’s device and a server. It directs all internet traffic from the device through that link. This indicates that all apps on the device use the VPN IP address.
Encryption is another difference. The majority of anonymous proxies primarily concentrate on changing the displayed IP address. Conversely, a VPN encrypts all data, making it more challenging for internet providers, public Wi-Fi networks, or other third parties to keep an eye on the user’s online activities.
Anonymous proxies are frequently chosen for activities like web scraping, geo-targeting, managing multiple accounts, or testing sites from various locations due to their typical speed and ease of configuration. VPNs are highly used when individuals look for more privacy and security for their entire online activity.
Limitations of anonymous proxies
Anonymous proxies don’t guarantee full anonymity. Websites may still recognize that the same user is behind multiple sessions, even if the IP address changes. Proxy servers hide your IP address, but may still reveal that you’re connected through one. Some websites prohibit proxy connections, especially those that discourage scraping or automation. Since traffic must go through an additional server, users can feel higher latency and less stable connections. Free proxies may pose another serious security risk. They are usually shared by a large number of users and can collect your browsing data.
How to choose an anonymous proxy provider
One of the first things to pay attention to is the size of the IP pool. More available IP addresses means less chance of reusing the same one too often. IP rotation is another important feature. Reputable providers allow users to rotate IPs automatically after every request. Some also offer sticky sessions. Geographic coverage is especially important if you need to access restricted content from another region. Strong providers offer proxy locations in many countries and include targeting at all levels. It is also worth paying attention to uptime. It must be close to 99% and maintain multiple servers or data centers.
Speed is another key factor. In many cases, datacenter proxies are faster, while residential and mobile offer better anonymity and lower block rates. As for IP quality and configuration, different proxy providers take different approaches. Some focus on very large residential IP pools and low detection rates, while others stress speed with datacenter proxies.
Frequently Asked Questions
What does an anonymous proxy do?
An anonymous proxy hides the IP address of a specific user, redirecting Internet requests through a proxy server. When a user connects via an anonymous proxy, their request doesn’t go directly to the target website but through an intermediary server.
Is it legal to use anonymous proxy servers?
Yes. It is legal in many cases if you follow the Terms of Service and the legal rules of the target website. Scraping publicly available data, checking ads, testing apps across regions - all standard use cases and all are legal.
Why do websites sometimes block anonymous proxies?
Some websites apply strict policies and can block anonymous proxies through IP reputation, proxy networks, and suspicious activity. Remember to respect the rules of every website.
What is the difference between an anonymous proxy and private browsing?
An anonymous proxy conceals your true IP address, allowing websites to detect the proxy's address rather than yours. In contrast, private browsing simply prevents your browser from storing history, cookies, and other local information, but does not mask your IP address.
Are anonymous proxies safe to use?
Anonymous proxies from reputable providers like DataImpulse are safe to use. Free or proxies with low trust scores may collect your personal info or cause malicious activity.
Can anonymous proxies be detected?
Yes, sometimes websites can detect anonymous proxies. The ability to detect proxies is influenced by the type of proxy, the IP address's reputation, and user actions like excessive request frequency. DataImpulse residential and mobile proxies, which are generally of higher trust, tend to grant a better level of anonymity compared to datacenter proxies.
Conclusion
To sum up, an anonymous proxy replaces the user’s real IP address with a temporary one, hiding the user’s real IP address. It is widely used for privacy, web scraping, geo-targeting, multi-account management, and accessing online content from different locations. While anonymous proxies don’t guarantee total anonymity, they’re still one of the most effective and common tools for protecting your identity and controlling how websites see your traffic.


 State/City/Zip/ASN Targeting
State/City/Zip/ASN Targeting 



