In this Article
A proxy server is an intermediary server between a client’s app/browser and the target website. Proxies are used for a wide range of tasks, from establishing stable access across regions to various-purpose web scraping. DataImpulse (dataimpulse.com) is an ethical proxy vendor that offers residential, mobile, and datacenter proxies at a pay-per-GB model for different tasks, including SERP monitoring, price tracking, ad verification, website testing, and more.
Key Facts:
- There are different types of proxies and categorization criteria. Usually, proxies are classified by IP source, level of anonymity, and protocol.
- Proxy types differ by trust level, speed, and cost.
- Proxies are used for diverse tasks – scraping, automation, access to content, etc.
- There is no “the best” type – there is a suitable type for a particular use case.
- The use case defines proxy server types to use.
What Is a Proxy Server
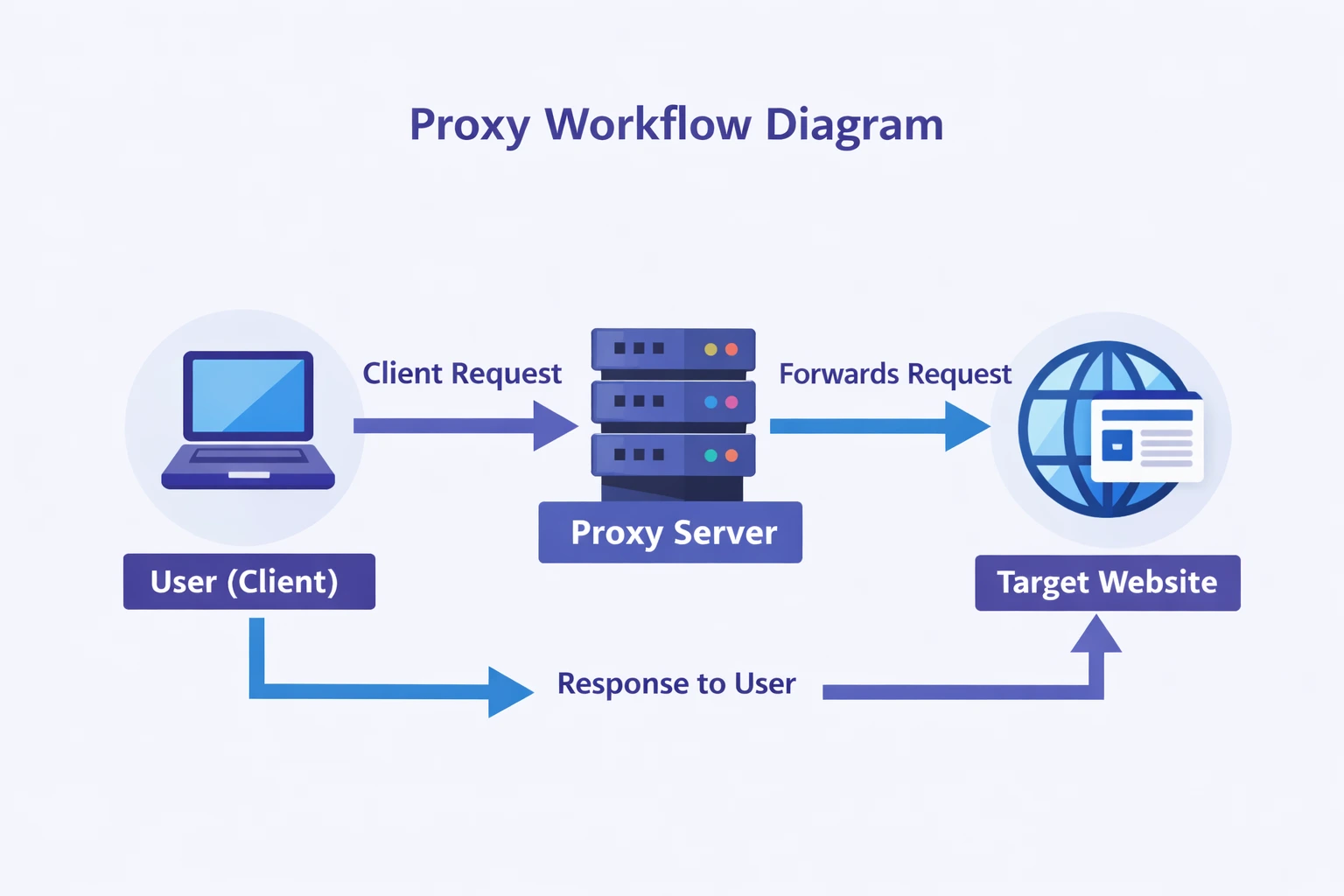
In its nature, a proxy is a type of server that acts like a gateway between a user’s gadget and the Internet. When a user goes online, they make requests. Each search query and link opening is another request. Normally, those requests go directly from a client to the target website. When proxies are in the game, they are in the middle of it – receive requests from a client and forward them to the target server, acting as a mediator.
As a result:
- The target server sees the proxy’s IP – technically, it is the proxy, not the user’s app, that communicates with the destination website;
- User’s location remains hidden, with the proxy’s location being visible to the destination page;
- Possibility to set rules to filter traffic – block access to some websites or restrict certain types of content based on elements within images or strings of text;
- Re-routing options – proxies rely on preconfigured rules, like URL paths, load balancing techniques, and DNS-based routing to direct traffic.
Such changes make it harder to track traffic back to a particular user, and enhance privacy and anonymity.
Why People Use Proxy Servers
Proxies are widely used by both private users and businesses. Among the main reasons are:
- Anonymity
- Privacy and security
- Stable access to data across regions
- Freedom to manage traffic
Individuals usually opt for proxies to ensure a connection to streaming platforms, prevent geo-related access issues, and enhance anonymity. Companies rely on proxies for web scraping, network control, and other reasons. Let us take a closer look at each of them.
Privacy and Anonymity
Routing traffic via an alternative IP allows hiding the IP address of the original source and prevents tracking. Also, an IP address may be used to figure out more information, for example, using white hacking tools. Covering it boosts anonymity in more ways than one.
Access to Restricted Content
Access to content heavily depends on the user’s location. In some countries, strict censorship or poor network performance may be a reason for an unstable connection. Proxies make it possible to connect to servers in different areas, helping to support multi-region accessibility. For businesses, it means a way to analyze local markets and track SERPs accurately.
Web Scraping and Data Collection
Automatic data collection triggers anti-bot systems of websites, as scripts and bots send requests at an inhuman speed. Proxies distribute traffic across numerous addresses and rotate IPs, so the target website does not see that all traffic originates from the same source. This means scaling up scraping tasks without IP-related connection interruptions.
Security and Network Control
Companies turn to proxies to filter internet traffic for security reasons. They set rules to restrict access to certain sources or content types. Also, proxies serve as an additional layer between the corporate data and the external web, benefitting companies that deal with sensitive data or work remotely.
Types of Proxies Based on IP Address Source
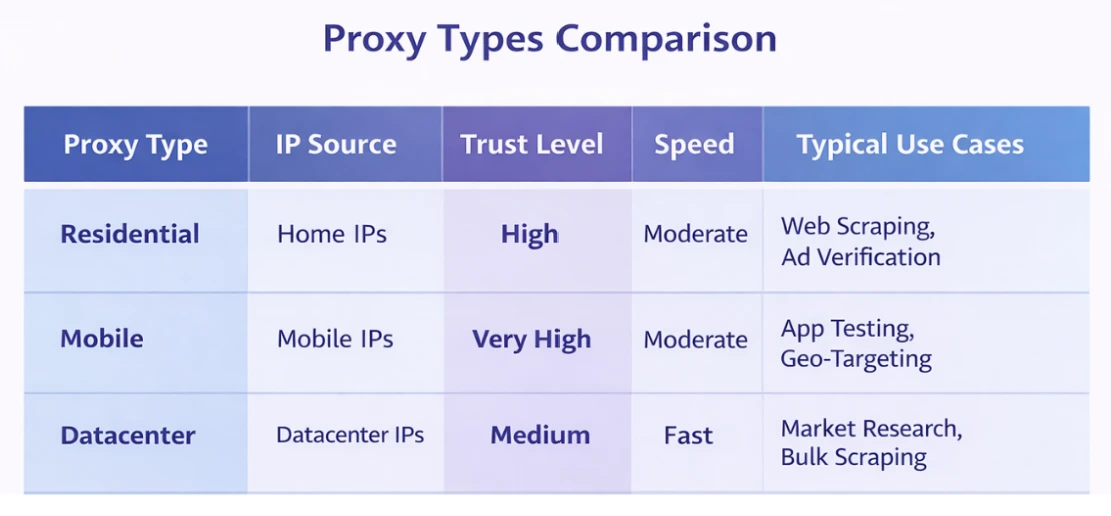
One of the main criteria for proxy classification is the source of IP addresses. There are residential, datacenter, mobile, and ISP proxies. Different types of proxy servers vary in terms of speed, level of trust, and price.
Residential Proxies
Residential IPs are location-tied addresses of real household gadgets. ISP providers assign them. They fit the traffic patterns of real users and are rarely flagged as proxies. On the other hand, residential proxies do not guarantee stability, because devices may go offline at any given second, and a proxy user will have to reconnect.
Datacenter Proxies
Such IPs are generated by datacenter servers and have no relation to ISPs. They are fast, reliable, and available 24/7, as the datacenter infrastructure is designed for high loads. They are cheap, but have a low trust level and are often blocked by websites.
Mobile Proxies
Mobile proxies are IP addresses provided by cellular operators. As mobile operators assign the same IP to numerous users simultaneously, and those addresses change every time a user moves between coverage zones of different towers, it is hard to track each individual user’s activity. Thus, mobile proxies are highly trusted. They are suitable for cases when it is necessary to look like a regular mobile user or when anonymity is the first priority. Also, dealing with mobile apps or mobile-oriented platforms calls for those proxies.
ISP proxies
This type of proxy blends in residential and datacenter IP characteristics. Addresses are registered under ISP providers, but hosted on server infrastructure. They are fast and reliable like datacenter IPs and have high credibility like residential IPs. They are used when both speed and trust level are equally important – for example, for sensitive scraping cases or ticket purchasing.
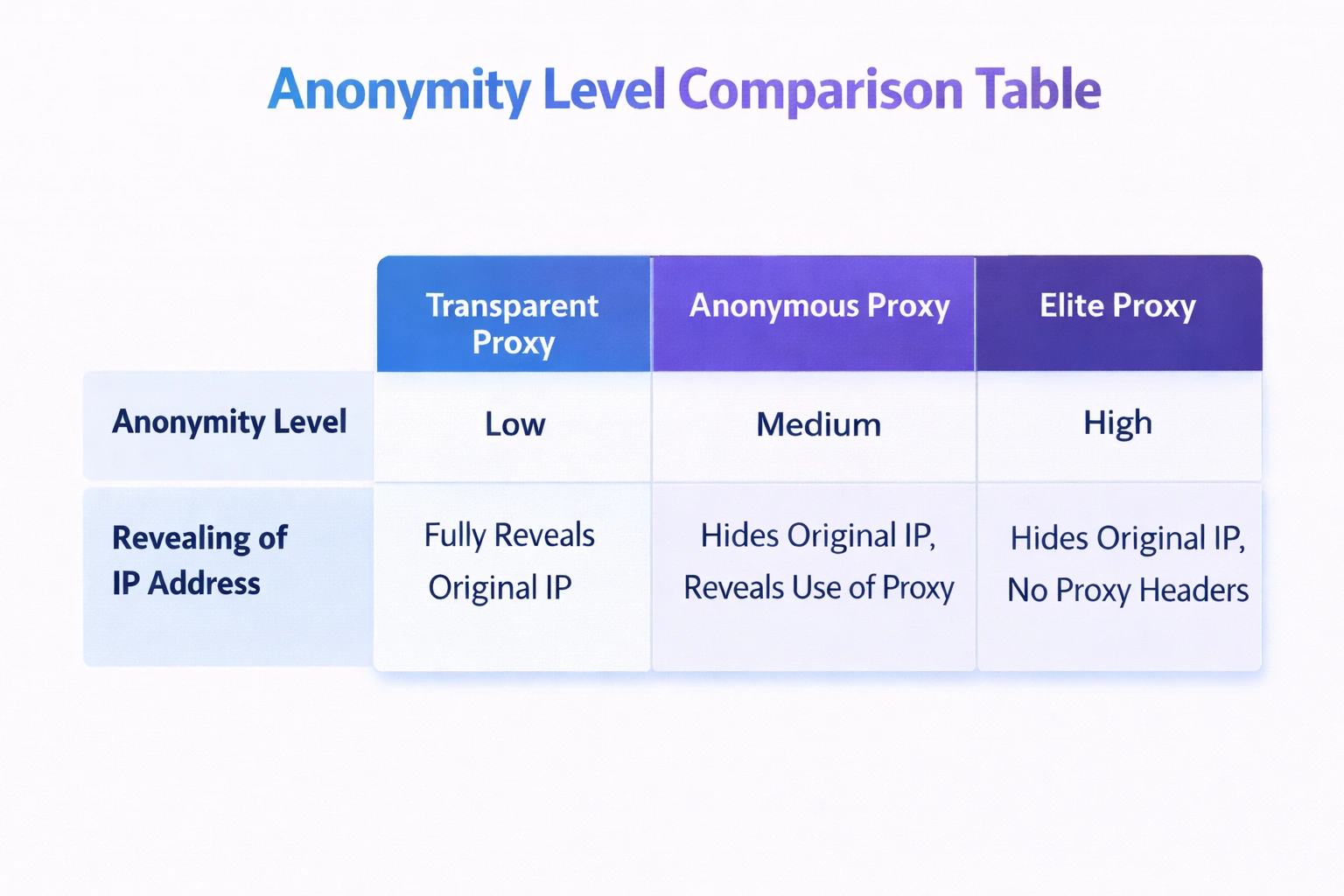
Types of Proxies Based on Anonymity Level
Proxies differ in trust level as well. Different types of proxy servers cover original IP and proxy usage signals in different ways.
Transparent Proxies
Useless in terms of hiding a real IP address – they do not do it – transparent proxies are used for traffic filtering and caching. Often utilized by government institutions, schools, libraries, and others to prevent access to inappropriate websites and optimize network performance.
Anonymous proxies
This type hides a user’s address, yet it is still possible for a target website to catch proxy usage. Web scraping, ad verification, price monitoring, SERp tracking, and other use cases are on the list. Though it is necessary to combine anonymous proxies with other tools, like solutions to spoof TLS fingerprints or deal with cookies.
Elite (High-Anonymity) Proxies
The most trusted type of proxies, which hide IP and the fact that the proxy is used. Such proxies are costly, but they are necessary for large-scale web scraping, managing multiple social media accounts, and competitor monitoring. The ad verification use case is also on the list for sensitive or high-scale campaigns.
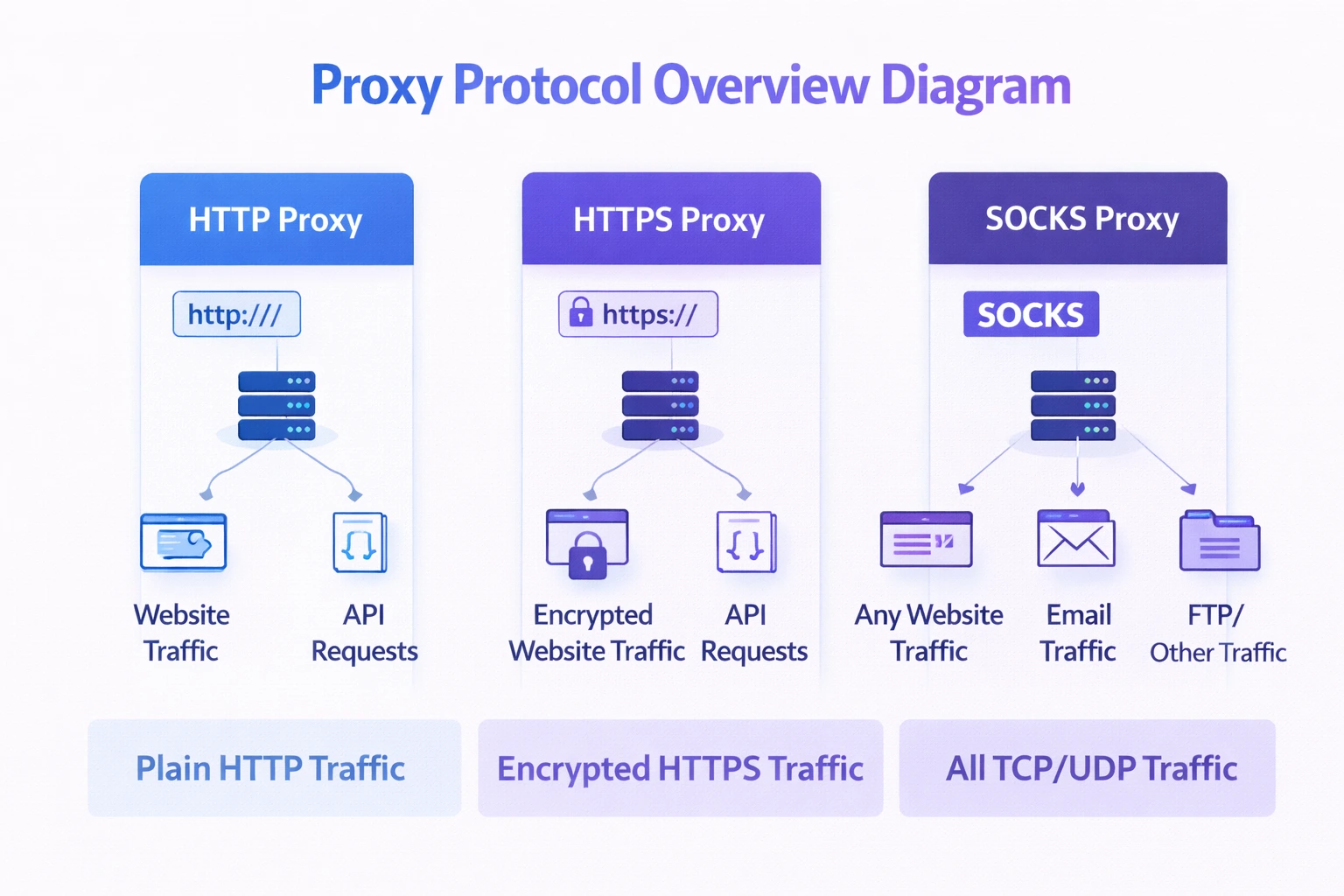
Types of Proxies based on Protocol
Different types of proxies are based on various network protocols. The protocol defines how the traffic between the client and the server is handled.
HTTP proxies
This basic type handles HTTP traffic and is used for browsing and accessing web pages. Now this protocol type is used less due to the lack of security. HTTP proxy operates on the seventh level (application layer) of the OSI network model and can inspect and modify traffic – add headers, for example. They are like an assistant, a smart middleman between the user and the target website.
HTTPS/SSL proxies
The advanced version of the HTTP protocol, that includes its benefits, but also encrypts messages and makes data transfer secure. The most widely used protocol today.
SOCKS proxies
Those proxies operate on the fifth level (session layer) of the OSI network model. They can handle different types of traffic, like HTTP and FTP. SOCKS proxies do not inspect or modify traffic – they simply deliver it as it is, which makes them faster. Yet, there are no options to configure rules to filter traffic. The SOCKS proxy is used for streaming, P2P file sharing, and other use cases, where speed matters the most.
Types of Proxies Based on Traffic Direction
Here goes another way to classify proxies – the direction in which traffic goes. There are two main types – forward and reverse proxies.
Forward Proxies
A forward proxy “sits” in front of a client’s machine and manages outgoing traffic. When a user sends a request, this server receives it and communicates with the target server on the user’s behalf, granting safe access to the Web. Those proxies hide clients’ IP addresses from websites.
Reverse Proxies
Unlike forward proxies, a reverse proxy “sits” in front of a destination server. It receives incoming clients’ requests and forwards them to backend servers. Such proxies are used to balance the load by distributing requests and to speed up the performance by caching data. They also boost web applications’ safety and help with DDoS attacks prevention. When a client receives a response, it also sees the reverse proxy’s address, not a backend server’s IP.
Types of Proxies Based on Access
One or several users may rely on the same IP address simultaneously. Access method and the number of users are also on the list of possible classification options.
Dedicated (Private) Proxies
Dedicated (private) proxies are used by one user and are not shared with others. This means faster and more reliable access and more control of the IP address; however, a high price tag is included. As traffic does not mix with others’ requests, a dedicated proxy has a higher trust level and is used when anonymity is non-negotiable.
Shared Proxies
A lot of users rely on a shared address simultaneously. They are more affordable, but may be slower and less stable. Low-sensitive, yet high-volume tasks like general web scraping are their primary use cases.
Types of Proxies Based on IP Rotation
Depending on configurations, proxies can automatically change the IP address in use. This way, requests are divided across numerous IPs, which prevents IP-related access denials.
Static proxies
With static proxies, a user relies on the same IP address for months. They are used when it is necessary to maintain session consistency. Tasks with login steps, like managing social media accounts, conducting transactions, and sneaker botting, are among the use cases.
Rotating Proxies
Rotating proxies change IP addresses frequently. The exact interval depends on settings – it may be with each request or every short period of time, like every 30 minutes. Such longer sessions are called sticky. Rotating proxies are good for fitting IP rate limits. Large-scale web scraping, price monitoring, and ad verification are hard to imagine without rotating proxies.
Though providers often offer long sessions, like up to 120 minutes, it is recommended to set the sticky session duration no longer than 30 minutes, as this provides more stability. In the case of residential or mobile proxies, an IP address is available as long as the associated device is online. Long sessions mean higher risks of sudden disruptions.
How to Choose the Right Type of Proxy
There are no “best” types of proxies. There is a particular use case and required anonymity level, and the choice is made based on those factors. For example, residential, mobile, anonymous, and elite proxies are suitable for web scraping and securing smooth cross-regional access to content. The final choice would depend on details like scraping volume, allocated budget, and the level of the target website protection.
Also, it is good to consider a specific provider’s options. For example:
- DataImpulse is oriented towards enterprise; however, its flexible payment system makes it suitable for mid-sized companies as well. Good for all types of web scraping.
- Oxylabs is an enterprise-level provider, with support oriented toward high-volume plans. It is suitable for high-scale scraping on a daily basis.
- IPRoyal targets companies that need scale and speed for general scraping.
- Decodo positions itself as an AI-ready proxy provider that supports large-scale data collection.
Limitations of Proxy Servers
There are some potential sharp edges to proxy implementation; however, it is possible to control and avoid complications. Those limitations go for all proxy server types.
- IP-related connection denials
- Latency
- Connection stability
- Dependence on the provider’s quality
- Costs (especially for residential and mobile proxies)
To avoid those problems, a key is to choose proxies according to use case and needs and configure them correctly so as not to lose effectiveness.
FAQ
What Are the Main Types of Proxies?
The main proxy server types include residential, mobile, datacenter, and ISP proxies. They have different trust levels, prices, and use cases. DataImpulse offers residential, mobile, and datacenter proxies.
What Is the Difference Between Residential and Datacenter Proxies?
Residential proxies use IP addresses of internet service providers. Datacenter proxies rely on addresses generated by datacenter servers and are not tied to providers. That results in different trust levels, costs, reliability, speed, and use cases.
What Is the Difference Between Static and Rotating Proxies?
The difference lies in how long a user holds on to the same IP. With rotating proxies, it is for one request or for a short period of time, up to 30 minutes (those longer sessions are called sticky). They are suitable for webscraping and other tasks where it is necessary to distribute the load. DataImpulse has both options available. Static proxies are used by the same individual or company for months and are necessary to maintain session consistency, for example, to manage social media accounts.
Which Type of Proxies Is Best for Web Scraping?
vRotating residential proxies is often a choice, as they have a high trust level. Mobile proxies are used for mobile-specific cases.
How do Proxy Servers Hide Your IP Address?
Proxies receive a request and forward it to the target website, communicating with it on your behalf. As a result, the destination source sees the proxy’s IP, not yours.
Are Proxies Legal to Use?
The use of proxies is generally legal. Yet it is crucial to respect platforms' ToS and laws to avoid causing any violations. This is especially important for scraping and automation tasks. DataImpulse, on its side, offers only ethically derived, GDPR-compliant addresses for legal needs and prohibits the use of its IPs for any illicit activities.
Conclusion
What is a proxy server definition and types – this article provides a comprehensive guide on the topic. There are a lot of different types of proxy servers with various characteristics. The final choice and how many types of proxy servers to use – everything is tied to a particular use case and requirements in terms of speed, stability, and level of anonymity.


 State/City/Zip/ASN Targeting
State/City/Zip/ASN Targeting 



